Breach: What It Means and Why You Should Care?
In the interconnected world of the internet, where we share everything from our cat videos to our credit card details, the term "breach" has become a constant shadow lurking in the digital alleyways. But what is a breach exactly, and why is it important?
Simply put, a breach is like a digital break-in. It occurs when sensitive data that should be protected is accessed by unauthorised parties. Imagine someone breaking into your online home and searching through your personal items.
Now, you might be thinking, "Who would want my data anyway?" Cybercriminals are pursuing a wealth of data, including your financial credentials and personal information. They can use this data for identity theft, financial fraud, or even to sell it on the dark web.
The consequences of a breach can be devastating, both for individuals and organisations. Imagine having your identity stolen, having your online accounts compromised, or having your hard-earned money disappear. That's the kind of nightmare scenario a breach can lead to.
Understanding the Different Types of Breaches?
There are various kinds of breaches, just as there are various kinds of burglaries. Here are the most common ones:
Data Breach: This is the most common type of breach, where cybercriminals gain access to sensitive data like names, addresses, passwords, and credit card numbers. Remember that time a big company lost millions of passwords? That was a data breach.
Security Breach: This is a broader term that encompasses any unauthorized access to a system or network. It could involve stealing data, disrupting services, or even taking control of entire systems.
Cloud Breach: With more and more data moving to the cloud, cloud breaches are becoming increasingly common. This is when attackers gain access to data stored on cloud servers.
How Do Breaches Happen?
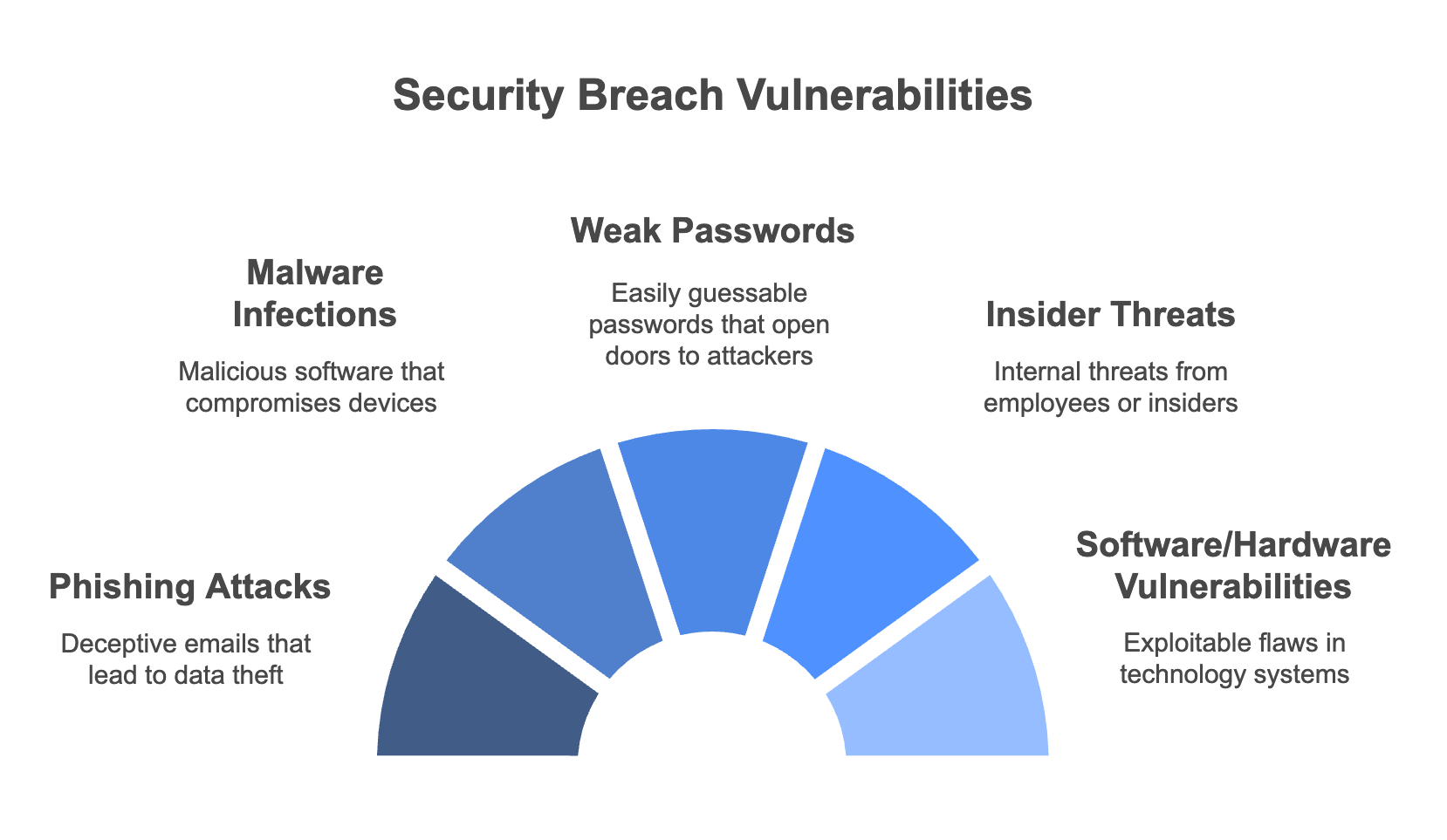
Breach incidents do not occur randomly. Attackers typically use particular vulnerabilities to obtain access. Here are some of the most common culprits:
Phishing Attacks: You know those emails that promise you a free iPhone or ask you to verify your bank account details? That's phishing. Clicking on those links or downloading those attachments can unleash malware that steals your data.
Malware Infections: Malware is like the common cold of the digital world. It can infect your devices through various means, from malicious websites to infected email attachments. Once inside, it can wreak havoc, stealing your data or even taking control of your device.
Weak Passwords: Using weak or easily guessable passwords is like leaving your front door wide open. Attackers can use automated tools to crack weak passwords and gain access to your accounts.
Insider Threats: Sometimes, the threat comes from within. Disgruntled employees or careless insiders can inadvertently expose sensitive data or even intentionally sabotage systems.
Vulnerabilities in Software/Hardware: No software or hardware is perfect. There are always vulnerabilities that attackers can exploit. That's why it's crucial to keep your software and hardware up to date with the latest security patches.
Signs of a Breach
Although the possibility of a breach cannot be totally eliminated, there are some warning indications that your data may have been compromised. Here are some red flags to watch out for:
Unusual Account Activity: If you see login attempts from unfamiliar locations, unexpected password changes, or transactions you don't recognize, it could be a sign of a breach.
Unfamiliar Software or Files: If you find new software or files on your device that you didn't install, it could be a sign of malware infection.
Suspicious Emails or Messages: Be wary of emails or messages that ask for personal information, contain suspicious links, or have attachments from unknown senders.
System Performance Issues: If your device suddenly becomes slow, crashes frequently, or displays unusual error messages, it could be a sign of malware infection.
What Happens After a Breach?
A breach can have serious repercussions for both people and organisations. Here's a glimpse of the potential fallout:
Financial Loss: Data breaches can lead to significant financial losses, from stolen funds to legal fees and regulatory fines.
Reputational Damage: A breach can tarnish an organization's reputation, leading to loss of customer trust and business opportunities.
Legal Implications: Organizations that fail to protect sensitive data can face legal action and hefty fines.
Loss of Customer Trust: For individuals, a breach can lead to identity theft, financial fraud, and a loss of privacy.
How to Prevent Breaches?
You can take precautions to safeguard your data and yourself, even though breaches are a real possibility. Here are some essential tips:
Strong Passwords and Multi-Factor Authentication: Use strong, unique passwords for each of your online accounts and enable multi-factor authentication whenever possible. Think of your password like your toothbrush – don't share it with anyone and change it regularly!
Regular Software Updates: Keep your software and operating systems up to date with the latest security patches. These updates often include fixes for newly discovered vulnerabilities.
Employee Security Awareness Training: Organizations should invest in security awareness training for their employees to educate them about cybersecurity threats and best practices.
Data Encryption and Secure Storage: Encrypt sensitive data both in transit and at rest. Use secure storage solutions like cloud services with strong encryption protocols.
What to Do if You're Breached?
Despite the best efforts, breaches can still occur. If you suspect your data has been compromised, here's what you should do:
Isolate Affected Systems: Disconnect the affected device from the internet to prevent further damage.
Contact Relevant Authorities: Report the breach to the relevant authorities, such as the police or your local cybercrime unit.
Notify Affected Individuals: If the breach involves personal data, notify the affected individuals as soon as possible.
Implement Damage Control Measures: Change passwords, monitor accounts for suspicious activity, and consider credit monitoring or identity theft protection services.

Frequently Asked Questions about Breaches
What is the difference between a data breach and a security breach? One particular kind of security breach that involves unauthorised access to private information is called a data breach. A security breach is a broader term that encompasses any unauthorized access to a system or network.
How can I protect myself from data breaches? Using strong passwords, turning on multi-factor authentication updating your software, and being wary of phishing scams and dubious emails are all ways to protect yourself.
What are the latest data breach statistics? Data breach statistics are constantly changing, but recent reports indicate that millions of records are compromised each year.
Are there any laws related to data breaches? Yes, many countries have laws and regulations in place to protect personal data and require organizations to notify individuals in case of a breach.