Algorithms
Algorithms are the unsung heroes of our technology-driven lives, working tirelessly behind the scenes to power everything from the apps on our smartphones to the complex systems that secure our digital world. But what exactly are algorithms, and why are they so crucial in today's interconnected society?
What is an Algorithm?
In essence, an algorithm is a set of step-by-step instructions designed to solve a specific problem or perform a particular task. It's like a recipe for a computer, guiding it through a series of operations to achieve a desired outcome. Just as a recipe guides you through baking a cake, an algorithm guides a computer through complex calculations, data processing, or decision-making.
Algorithms aren't limited to computers, though. We use them in our everyday lives, too. Following a recipe to cook, using a map to navigate, or even tying your shoelaces – these all involve following a set of steps, which is essentially an algorithm.
Key Characteristics of Algorithms:
Well-defined: Each step in an algorithm must be clear and unambiguous, leaving no room for interpretation.
Finite: An algorithm must have a finite number of steps and terminate after a finite amount of time.
Effective: An algorithm must produce the correct output for any valid input.
Independent: An algorithm should be independent of the specific programming language or hardware used to implement it.
Why are Algorithms Important?
Algorithms are fundamental to computer science and have revolutionized countless fields:
Automation: Algorithms enable computers to automate repetitive tasks, freeing up human time and resources for more creative and complex endeavors.
Data Processing: Algorithms are essential for processing and analyzing vast amounts of data, extracting meaningful insights, and making informed decisions.
Problem Solving: Algorithms provide a systematic approach to solving complex problems, breaking them down into smaller, more manageable steps.
Efficiency: Well-designed algorithms can optimize processes, improving efficiency and reducing resource consumption.
Innovation: Algorithms are at the heart of many technological innovations, from artificial intelligence and machine learning to self-driving cars and personalized medicine.
Algorithms in Cybersecurity:
Algorithms play a critical role in safeguarding our digital world, powering a wide range of security solutions:
Encryption Algorithms: These algorithms protect sensitive data by converting it into a code that can only be deciphered with the correct key, ensuring confidentiality and integrity.
Intrusion Detection Systems: Algorithms analyze network traffic to identify suspicious patterns and potential security breaches, helping to prevent unauthorized access and malicious activity.
Antivirus Software: Algorithms power the detection engines of antivirus software, identifying and neutralizing malware based on signatures, heuristics, and behavioral analysis.
Fraud Detection: Algorithms analyze financial transactions and user behavior to detect fraudulent activities, protecting individuals and organizations from financial losses.
Security Auditing: Algorithms assist in security audits by analyzing logs, identifying vulnerabilities, and assessing security risks.
Types of Algorithms:
There are countless types of algorithms, each designed for a specific purpose. Some common categories include:
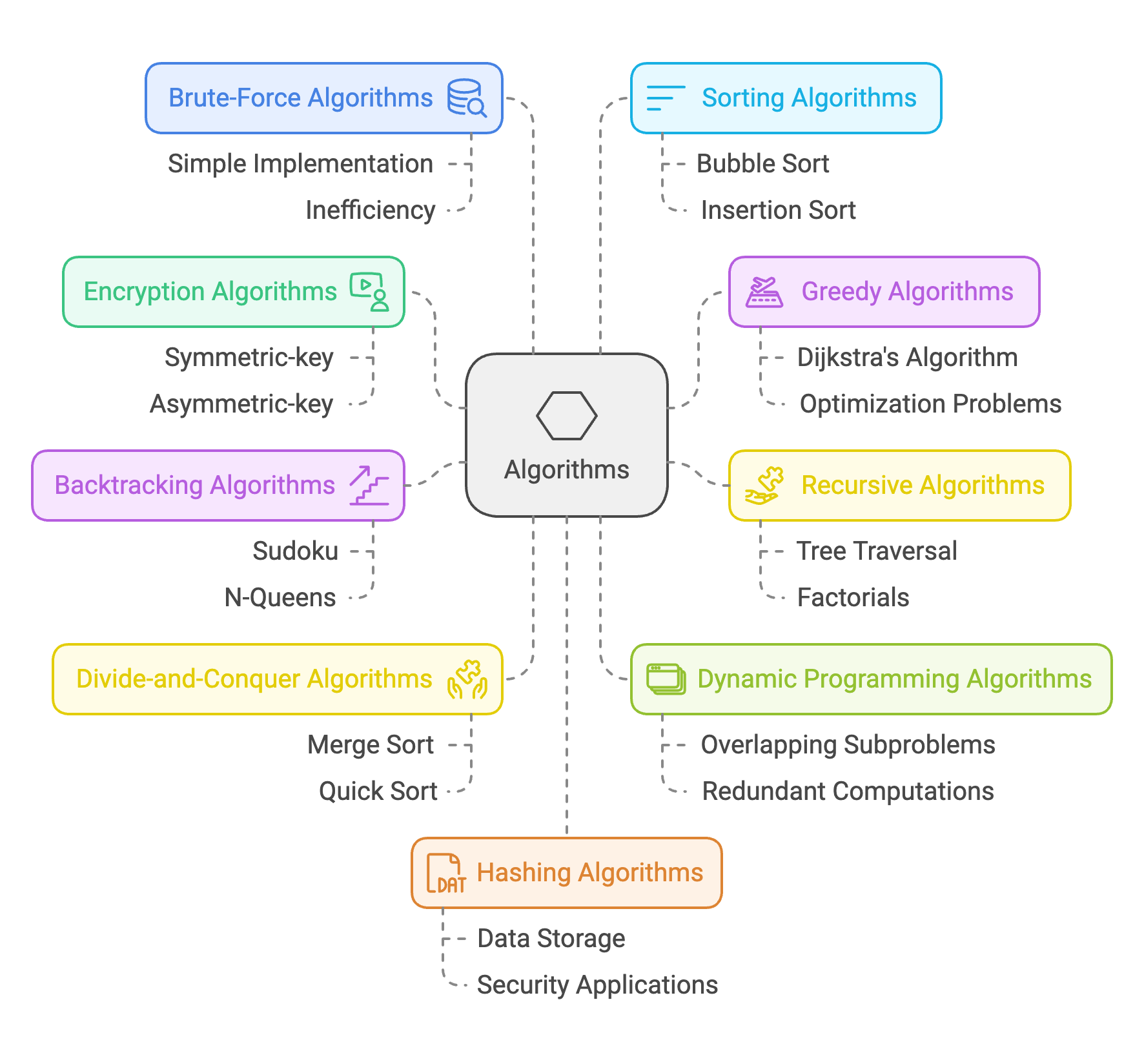
Search Engine Algorithm: This is a complex set of algorithms that power search engines like Google. They take your search query (keywords and operators) as input, analyze billions of web pages, and rank them based on relevance, authority, user experience, and many other factors. This ensures that the most relevant and useful results appear at the top of the search results page.
Encryption Algorithm: Encryption algorithms are essential for protecting data confidentiality and integrity. They transform data into a coded format that can only be deciphered with the correct key. There are two main types:
Symmetric-key algorithms: Use the same key for both encryption and decryption (e.g., AES, DES).
Asymmetric-key algorithms: Use separate keys for encryption and decryption (e.g., RSA, ECC).
Greedy Algorithm: These algorithms make locally optimal choices at each step with the hope of finding a global optimum. They are often used for optimization problems but don't always guarantee the absolute best solution. A classic example is Dijkstra's algorithm for finding the shortest path in a graph.
Recursive Algorithm: A recursive algorithm solves a problem by calling itself repeatedly with a smaller subproblem until it reaches a base case that can be solved directly. This approach is often used for tasks like traversing tree structures or calculating factorials.
Backtracking Algorithm: Backtracking algorithms solve problems by trying to build a solution incrementally, one piece at a time. If a path leads to an incorrect result, the algorithm "backtracks" and tries a different path. This is commonly used for problems like solving Sudoku puzzles or the N-Queens problem.
Divide-and-Conquer Algorithm: This approach breaks down a problem into smaller subproblems that are easier to solve, solves them recursively, and then combines the solutions to solve the original problem. Examples include merge sort and quick sort.
Dynamic Programming Algorithm: Dynamic programming algorithms solve problems by breaking them down into overlapping subproblems and storing the solutions to avoid redundant computations. This is often used for optimization problems where the same subproblems are encountered multiple times.
Brute-Force Algorithm: This straightforward approach tries all possible solutions to a problem until a solution is found. While simple to implement, it can be very inefficient for complex problems.
Sorting Algorithm: Sorting algorithms arrange data in a specific order, such as ascending or descending. There are many different sorting algorithms, each with its own trade-offs in terms of efficiency and complexity (e.g., bubble sort, insertion sort, merge sort, quick sort).
Hashing Algorithm: Hashing algorithms take data of any size and convert it into a fixed-size string of characters (a hash). This is often used for data storage, retrieval, and security applications.
Randomized Algorithm: These algorithms use randomness as part of their logic. They can be helpful in situations where deterministic algorithms are difficult to design or when a problem requires an element of unpredictability.
Algorithms in Everyday Life:
Algorithms are deeply embedded in our daily lives, often without us even realizing it:
Social Media Feeds: Algorithms determine which posts you see on your social media feeds based on your interests and interactions.
Search Engine Results: Algorithms rank websites in search results based on relevance, authority, and other factors.
Online Shopping Recommendations: Algorithms suggest products you might be interested in based on your browsing history and purchase patterns.
Navigation Apps: Algorithms calculate the fastest or most efficient route to your destination, taking into account traffic conditions and other factors.
Streaming Services: Algorithms recommend movies, TV shows, or music based on your viewing or listening preferences.
The Future of Algorithms:
As technology continues to evolve, algorithms will play an even greater role in shaping our world. They will drive innovation in fields such as artificial intelligence, robotics, and biotechnology, leading to new discoveries and solutions to complex problems.
However, it's important to be mindful of the ethical implications of algorithms. As algorithms become more sophisticated, they can perpetuate biases, invade privacy, or even be used for malicious purposes. Therefore, it's crucial to develop and deploy algorithms responsibly, ensuring fairness, transparency, and accountability.
By understanding the power and potential of algorithms, we can harness their capabilities to improve our lives, enhance security, and create a better future.